Discover Every AI Agent Your Organization Builds, Across Every Major Cloud Platform

Lasso now natively integrates with AWS Bedrock, Microsoft Azure AI Foundry, Microsoft Copilot Studio, Google Vertex AI, and more to automatically discover, inventory, and profile every low code no code AI agent in your environment, whether it was built by an engineering team or configured by a business unit with a no-code tool.
The AI Discovery Problem
AI agent discovery remains the most common gap security teams report, and it is getting harder as organizations move from using AI tools to building their own agents.
Using a third-party AI tool means accepting someone else's security model.
Building an agent means owning the model selection, the system prompt, the tool access, the guardrails, and the behavior at runtime. Security teams need to know what their organization is building, not just what it is subscribing to.
The agents being built today are not all coming from engineering teams writing code.
A compliance team might use Microsoft Copilot Studio to build an internal agent that queries HR data and summarizes policy documents while the engineering team might use AWS Bedrock to build a customer-facing support agent with access to a production database.
Each of these agents has a different model, a different tool surface, a different set of permissions, and a different risk profile. None of them live in the same place, and the platforms themselves do not provide cross-environment visibility.
Security teams need a single, continuously updated view of every agent being built and deployed across the organization, for internal use and for external-facing purposes.
That is what discovery provides, and it is the first step in Lasso's AI security lifecycle of discovery, AI risk assessment and runtime protection.
The Solution: Discover AI Agents No Matter Where They Run
NEW! Low Code No Code Agent Builders
The fastest-growing source of new agents in most organizations is not engineering. Business teams are building agents directly in managed cloud platforms and third-party tools without writing a line of code. Lasso connects natively to the platforms where enterprise low code no code AI agents are being built at scale:
- AWS Bedrock
- Microsoft Azure AI Foundry
- Microsoft Copilot Studio
- Google Vertex AI
- Salesforce Agentforce
- & more
AI Workloads in Cloud Environments
Not every organization building AI applications in the cloud uses a managed AI service. Many are assembling agents directly inside their cloud environment, in Google Cloud, AWS, or Azure, without ever touching Vertex AI, Bedrock, or Foundry. Lasso connects to every cloud environment to surface and discover agents and applications that would otherwise have no path into a security inventory.
CI/CD Pipelines and Code Repositories
Lasso scans repositories and CI/CD pipelines to discover homegrown agents at the point they are being built, before they reach production, and catalogs them alongside everything found in cloud environments and no-code platforms.
The AI-BOM
Lasso discovers and catalogs every AI agent and application built by an organization.
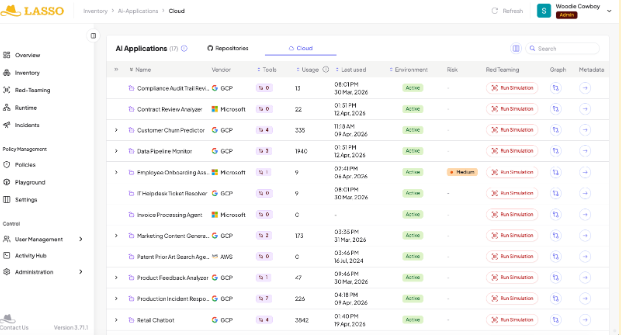
For every discovered agent, it generates an AI Bill of Materials (AI-BOM): a structured record of every component that defines what the agent is, what it can do, and what it is connected to.
The AI-BOM covers:
- The foundation model and version
- The system prompt
- Every connected tool and MCP server
- APIs
- Retrieval sources the agent can invoke
- The guardrails and output policies configured
- The orchestration framework in use (LangChain, LlamaIndex, AutoGen, CrewAI, and others)
- The full dependency set across libraries and third-party components
The AI-BOM is not a point-in-time export and updates continuously as the agent evolves. This means that when the system prompt changes, a new tool is added, or there is a model version update, all of it is reflected in the inventory automatically.
AI-SPM: The Security & Dependencies Graph
Alongside the AI-BOM, Lasso generates a dependency graph that maps every agent to its connected components, like the models, databases, APIs, sub-agents, and external services. For multi-agent architectures, the graph traces delegation chains and shows where permissions propagate and where authorization boundaries are defined or absent.
From that graph, Lasso runs static analysis and flags security gaps directly against the configured architecture. The findings cover two layers to ensure agents are secure by design:
- Based on the business logic of how the agent was written: whether its defined scope is coherent, whether its system prompt creates contradictions with its tool access, and whether its guardrails cover the actual risk surface.
- Based on individual components: a tool that performs a web fetch with no guardrails on the return path, a sub-agent with permissions that exceed what the parent agent should be able to delegate, or a database connection with no access boundary defined.
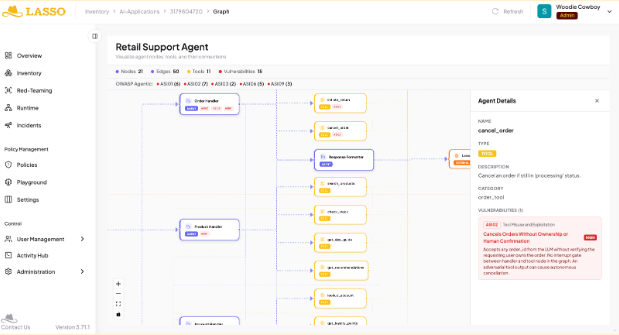
Every finding is mapped to OWASP and agentic vulnerability frameworks, so security teams can see not just what is misconfigured but what level of attack that misconfiguration enables.
Model Access Control and Governance
Discovery is also the foundation for governing how agents are built, and with this inventory, security teams can enforce policies on model usage across the organization, including which foundation models are approved for internal agents, which are approved for external-facing agents, which are restricted entirely, and which technology stacks and orchestration frameworks are within policy.
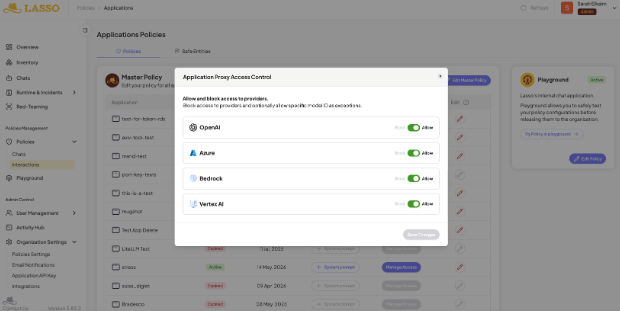
This matters because the choice of model is a security decision. Without visibility into what models are being used to build which agents, those decisions get made by individual teams without security input.
Lasso’s AI Discovery: Part 1 of the AI Security Lifecycle
Lasso’s AI discovery is the first step in its AI security lifecycle framework, which has 3 main components: discovery, AI risk assessment, and runtime protection.
AI Risk Assessment
Once discovered, and directly from the inventory, security teams can run Lasso's Automated AI Red Teaming against any agent. Posture findings feed directly into red team targeting, so adversarial testing is run against the actual risk surface. Lasso first reverse engineers the agent through reconnaissance and finds out the model, system prompt constraints, tool call sequences, and guardrail limits. That reconnaissance determines what gets attacked and at what depth.
Lasso offers 3 attack modes for Red Teaming:
- Static, single turn attacks using over 3,000+ different attack types and obfuscation techniques
- Multi-turn attacks that continuously probe the application to reveal sensitive information or partake in subject drift
- High agency, bespoke attacks, which are tailored attacks to discover the fragile intent of the agent
Every red teaming finding maps to a direct remediation, with Lasso manually or automatically creating specific inline guardrail updates and conducting a re-test to confirm the fix.
Runtime Protection
Lasso enforces inline policy at the proxy, API, or AI Gateway layer with real-time blocking under 50ms. Policies are also generated from posture analysis and red team findings, so vulnerabilities identified in testing automatically produce guardrail updates that feed into runtime enforcement without a manual handoff.
In addition, Lasso's intent security engine monitors every agent interaction continuously, building a behavioral baseline from full interaction history and measuring each action against it to detect and respond to zero day AI threats.
It Starts with Discovery
Every stage of the AI security lifecycle, from posture analysis and red teaming to runtime protection, depends on knowing what agents are in the environment and how they are built. Lasso connects to your cloud platforms, builds the inventory, and from that point the full lifecycle runs continuously without requiring manual input between stages.
If you are building AI agents, book a demo to see what Lasso finds in your environment.
FAQs




.png)