Discovery & AI-BOM
Discover every agent and AI application across your environments, consolidate them into a single inventory, and assess risk across the full agentic ecosystem.

AI Visibility Remains the Number One AI Security Challenge
As AI applications are built and deployed across the enterprise, security teams are losing the ability to track what exists, what agents connects to, and how they behaves.
Inventory Every AI Component
Security teams need more than a list of applications. They need to know every model, system prompt, agent, tool, and framework in use, where it runs, who owns it, and all the data required to properly discover and manage it.
Map How Agents Connect
Visualizing every agent as a graph, with its connections to MCPs, databases, LLMs, and internal services, gives security teams the architectural visibility needed to identify potential attack paths before they can be exploited.
Continuously Track Every Update
As AI applications evolve with changing business needs, security teams need an inventory that updates automatically through native integrations in order to assess AI risks, govern and enforce guardrails, and respond to incidents.
Full Stack Visibility into Every AI Agent with Lasso
Lasso automatically discovers every AI agent and application across your environment, maps how they are built and connected, and keeps your inventory current with every change, giving security teams a single source of truth for governing agentic AI from code to runtime.
Discover Every Agent and AI Application
Discover every AI application across your environment, regardless of where it runs. Identify the owner, the LLM in use, the system prompt, policies, tool registry, and guardrails, and keep it current with every deployment change.
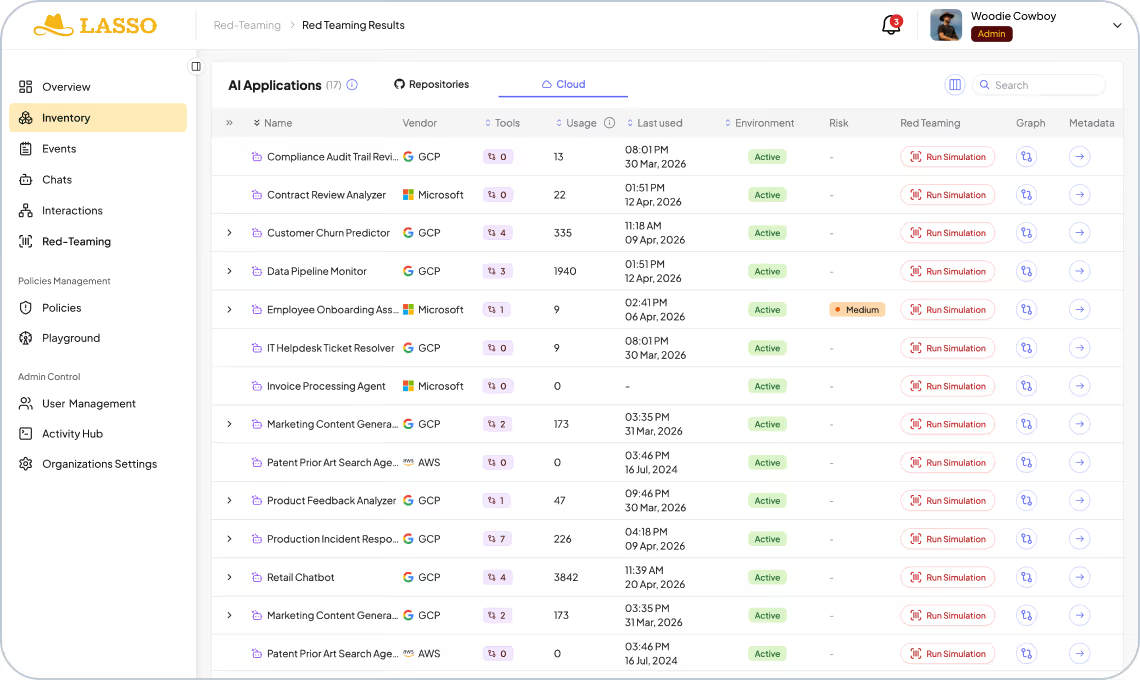

Catalog Your AI Assets
Inventory every AI component, including models, MCP servers, delegated agents, databases, third-party tool connectors, identity boundaries, and authorization policies to assess risk and manage compliance and supply chain integrity.
Map the Full Dependency Graph
Visualize every AI application and its connected sub-agents, LLM, database, APIs, MCPs, and more. Understand delegation chains and see where permissions or authorization boundaries are missing, thereby mapping OWASP risks and agentic vulnerability frameworks across the supply chain.

Surface Risks Across the AI Lifecycle
Monitor every AI interaction and identify the most vulnerable applications, track incident trends over time, and maintain the decision-level traceability needed for governance and auditability across the full AI lifecycle.
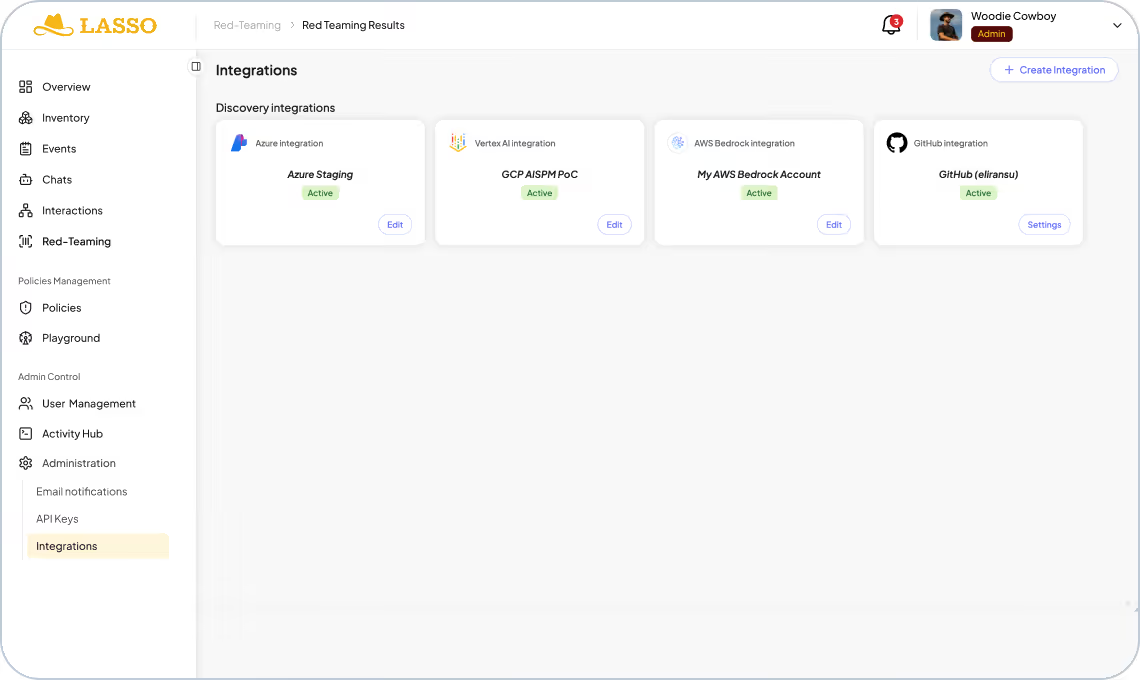
Connect to Every Platform Where AI Runs
Automatically identify every AI workload running in your cloud environments, along with new agents or configuration change through native integrations with CI platforms and low code no code agent builder platforms, like Amazon Bedrock, Azure AI Foundry, Microsoft Copilot Studio, Google Vertex AI, Salesforce Agentforce.

The Lasso Advantage
Built for the agentic era.
CI-Native
Security keeps pace with engineering.
100%
OWASP & NIST mapping
1 click
Automated red teaming
100%
Discovery of AI assets
7 min
Discovery time for new agents

Zero Deployment
Agentless, read-only integration into CI pipelines and native integrations with cloud providers and third-party agent builder tools.

Explore the Lasso Platform
Securing autonomous AI agents, LLM applications, and agentic workflows from build-time through runtime.
Platform Overview
Discovery & AI-BOM
Discover and map every agent in your ecosystem by integrating with your CI/CD pipelines, cloud providers, and third-party agent builders.
AI Security Posture Management
Enable security by design agents by mitigating supply chain risks and agent misconfigurations and creating out-of-the-box or custom hardening policies.
Automated AI Red Teaming
Stress-test application logic through static, multi-turn, and high-agency attack to uncover vulnerabilities and build adaptive guardrails.
AI Detection & Response
Monitor every agent and application at runtime to automatically detect and respond to AI threats and policy violations.

FAQs
How does Lasso consolidate AI agents built across different platforms into one inventory?
AI agents are being built across cloud platforms, internal codebases, and third-party agent builders simultaneously, often by different teams with no central visibility. Lasso connects natively to each of these environments and pulls every discovered agent and application into a single continuous inventory, regardless of where it was built or where it runs. Security teams get one place to see everything, without requiring teams to self-report or manually register what they have built.
What is an AI-BOM?
An AI Bill of Materials is the agentic equivalent of a software BOM, extended to capture the components that define how an AI application behaves and what it can do. Where a traditional SBOM tracks libraries and dependencies, an AI-BOM captures the model in use, the system prompt, the tools and MCP servers the agent can invoke, the databases and external services it connects to, its guardrails, and the authorization policies governing its actions. It is the foundational artifact for understanding what an AI application is made of and assessing the risk that configuration introduces.
How does Lasso keep the inventory current as applications change?
Lasso connects to your CI pipeline and cloud platforms so that every code change, configuration update, or new deployment automatically updates the inventory. There is no manual process and no risk of working from a stale snapshot. Security teams always have an accurate view of what is running and how it is configured.
How does Discovery fit into our broader AI security program?
Discovery is the first step in Lasso's full governance lifecycle for agentic AI. Once you have an accurate inventory of your AI applications and agents, Lasso takes you through risk assessment, security testing, and runtime protection. This means your security program covers the entire lifecycle from the moment an agent is built through to its operation in production.
Keep up with Lasso