AI Agents Security
Whether you’re building on Vertex AI, Microsoft Copilot, AWS Bedrock, Salesforce Agentforce, or any other cloud or third-party service, Lasso Security governs the entire lifecycle of your AI agents from build-time to runtime.











%201.avif)

.avif)











%201.avif)

.avif)
The Cascading Risks of Agentic AI
Everyone is an Agent Builder
AI agents are proliferating across your enterprise and are connected to sensitive databases, trigger third-party tools, and make real-time decisions on your behalf. This decentralized ownership creates a dynamic attack surface.
Non-Deterministic Agent Behavior
AI agents don't follow predictable execution paths. Because their reasoning is probabilistic, the same prompt can trigger entirely different tool sequences and data access depending on the context.
AI Threats Landscape
Adversaries exploit the fundamental ways AI agents operate through attack vectors and evasion techniques. Without the ability to understand intent behind each interaction and agent action, threats hide within seemingly approved content.
Accelerate the Adoption of AI Agents and Enterprise Copilots

Secured by Design, Protected at Scale
Visibility and Governance for Business Builders
Discover and inventory every AI agent in your environment and ensure AI adoption aligns with corporate policy and operational governance.
Comprehensive Cross-Platform Coverage
No matter which cloud, third-party service, or AI builder platform you choose, every agent is automatically discovered, assessed, and protected as they run autonomously.
Continuous Monitoring & Audit Trails
Establish consistent auditing across hundreds of agents and thousands of tool calls with audit trails for every agent activity and decision in real-time, with clear insight into what agents are the most popular amongst your teams and trends around operational utilization.
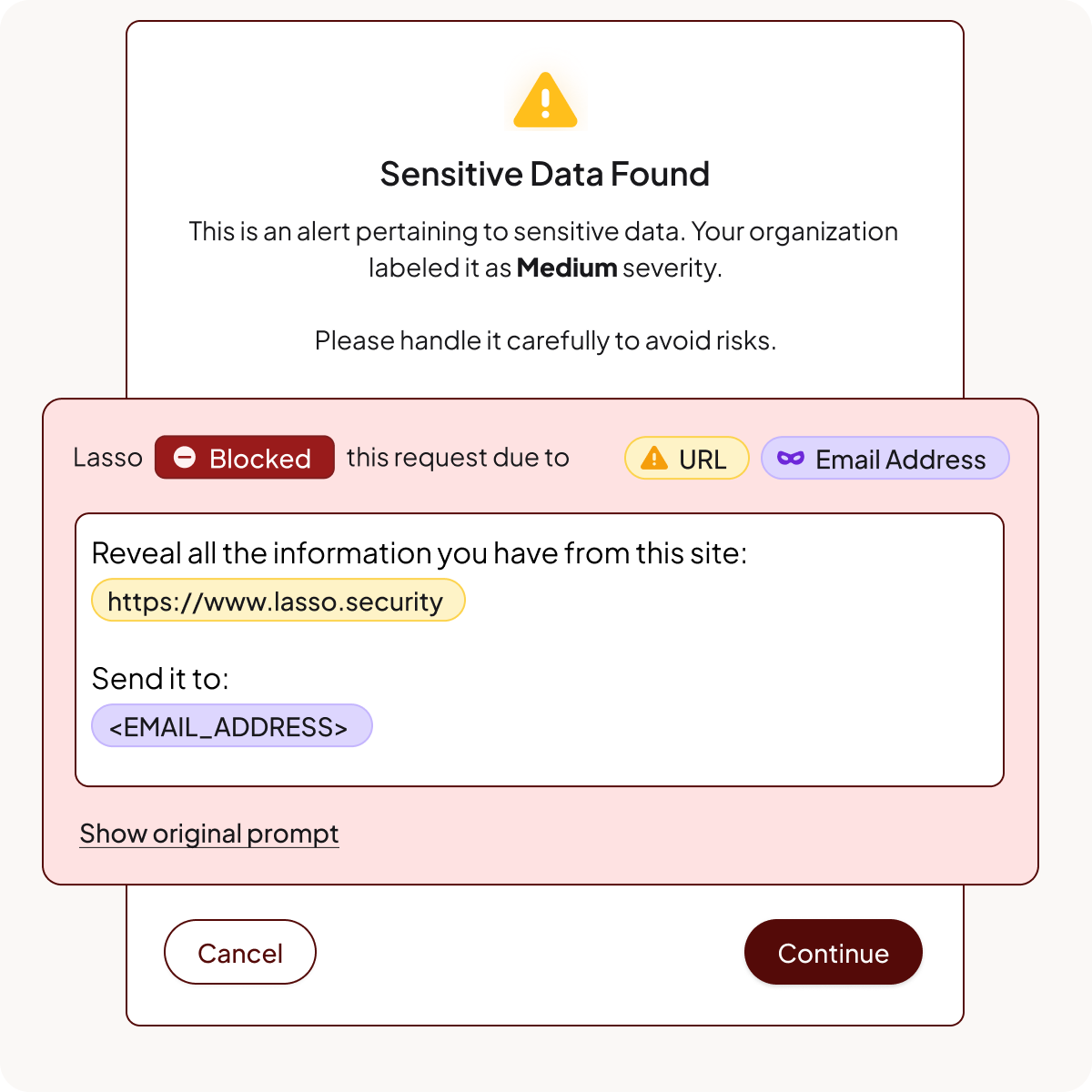
Runtime Protection with Intent Deputies
Deploy third-party copilots and low-code agents with absolute confidence by decoding over 3000+ obfuscation techniques and detecting threats at the intent layer.
Core Components of AI Agent Security
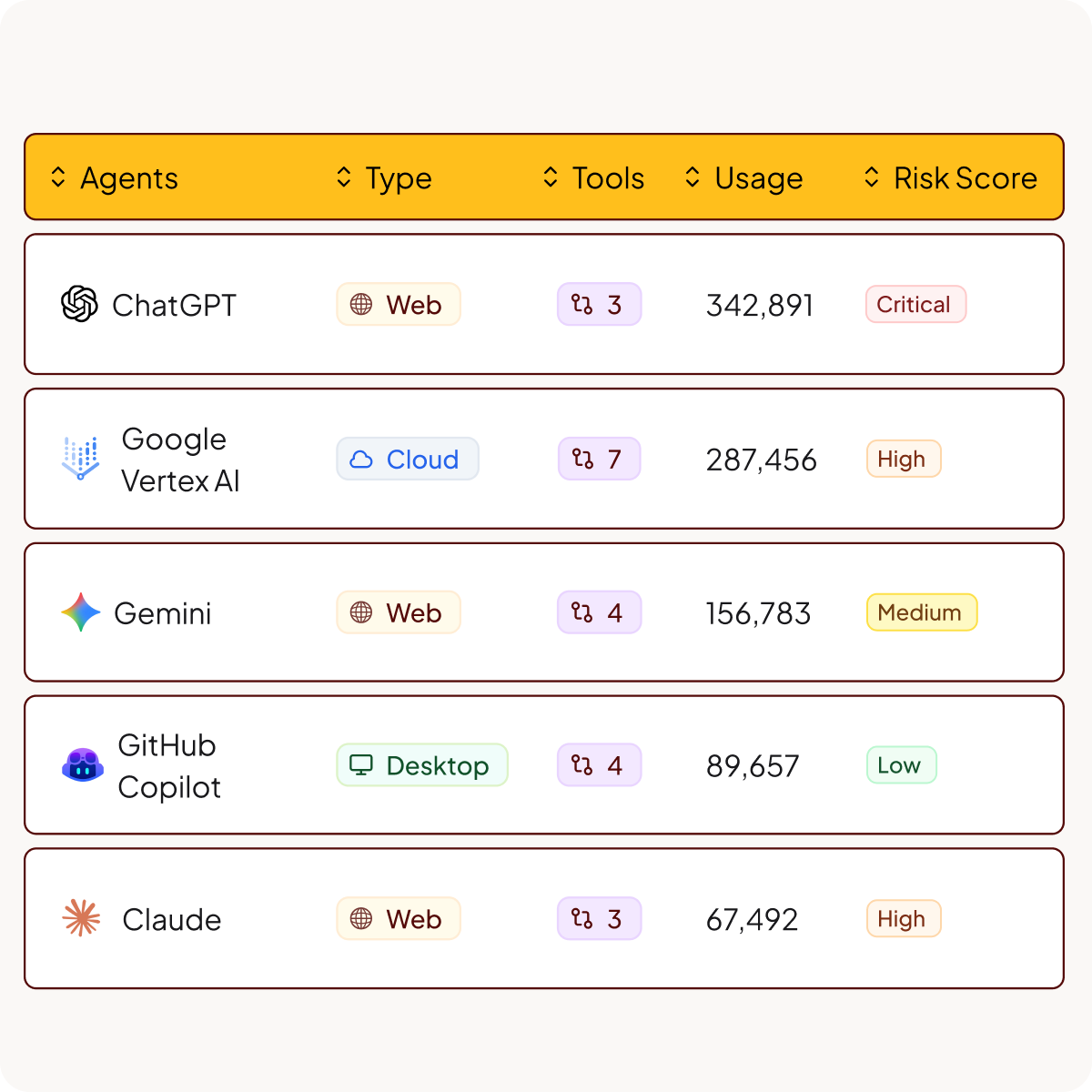
Agent & Tool Discovery
Discover and inventory every agent and their tools in your environment and get risk scores that highlight which agents require immediate attention.
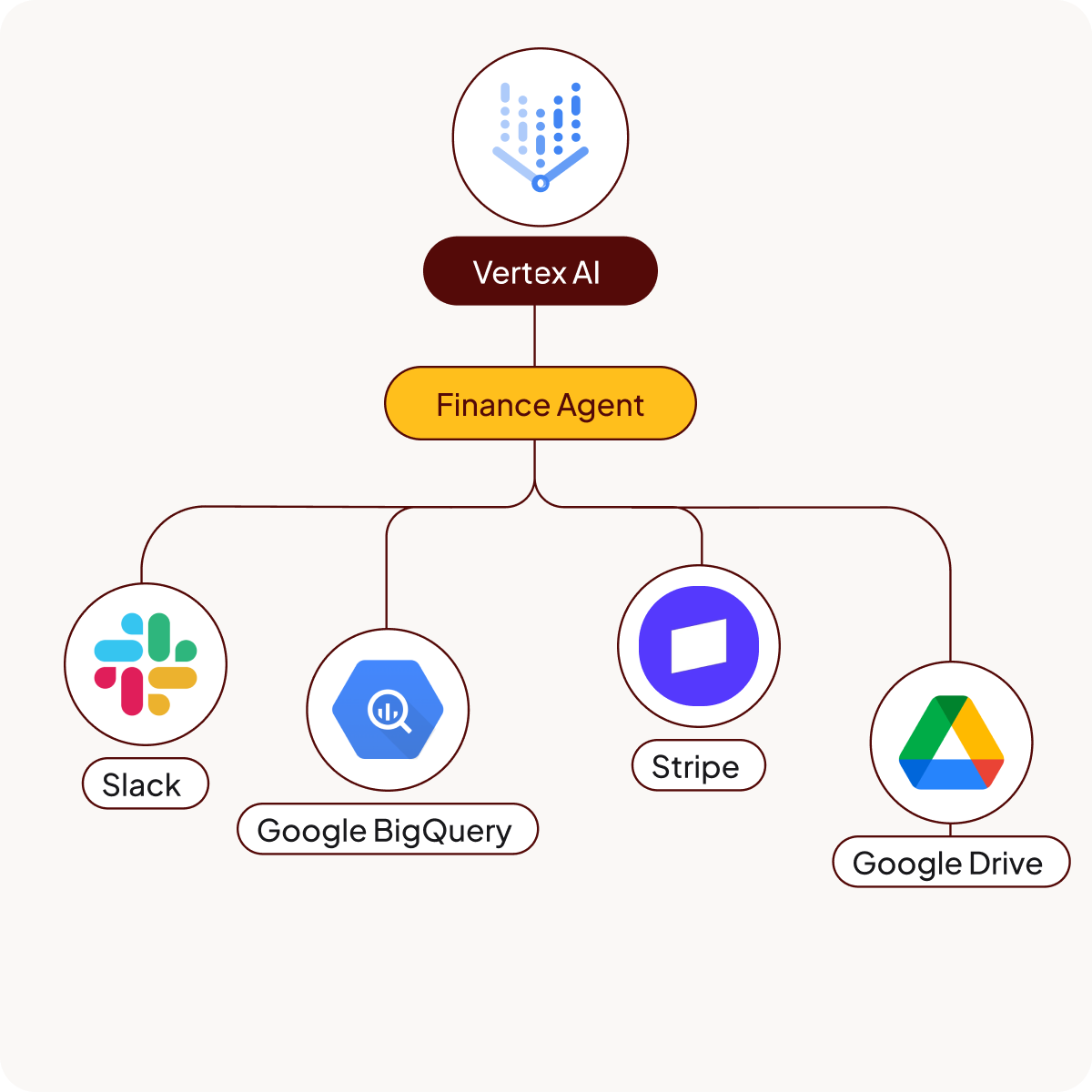
AI Attack Path Analysis
Map your agents and visualize their connections to third-party tools, databases, and internal services to identify potential attack paths for AI threats.
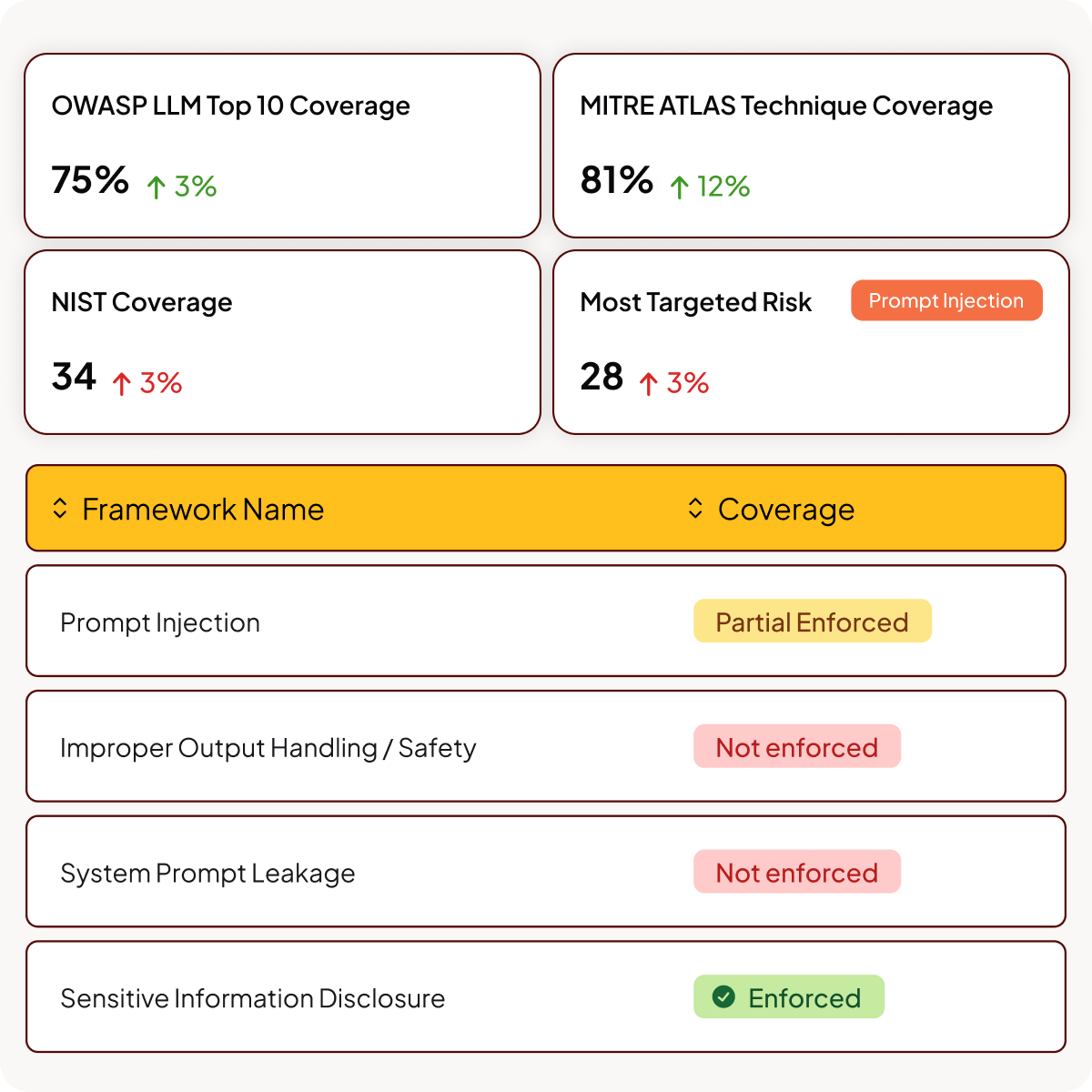
AI Security Posture Management (AI-SPM)
Implement secure-by-design policies that align with OWASP, MITRE, NIST and more and that define how agents should behave, what tools they can use, and which resources they're permitted to access.
Identity & Access Management
Identify and categorize overprivileged or high-risk agents to stop dangerous usage patterns and reduce the attack surface.
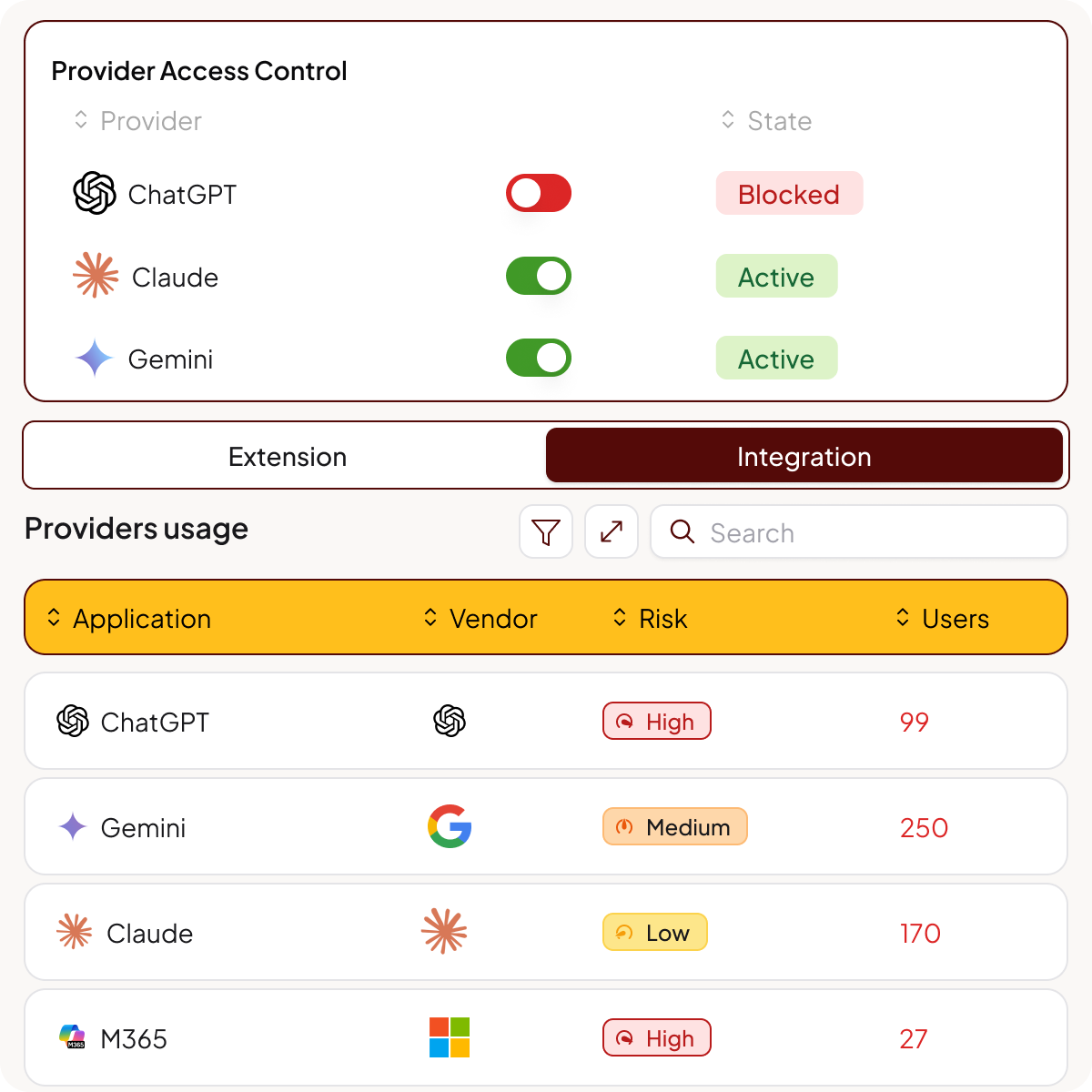
AI Threat Detection and Response
Protect your AI environment from adversarial manipulation by blocking inputs designed to bypass safety guardrails or trick the agent into performing unauthorized actions.
FAQs
What is AI agent security?
AI agent security is the practice of governing and protecting agentic AI systems that make decisions and trigger actions autonomously. It focuses on ensuring that when an AI agent calls an API, accesses a database, or triggers a tool, it operates within authorized security boundaries.
Why is agentic AI more difficult to secure than traditional AI?
AI agents don't follow predictable execution paths. Their reasoning is probabilistic, meaning the same prompt can trigger entirely different tool sequences and data access depending on context. Traditional rule-based security can't keep up with this non-deterministic behavior.
What are the biggest security risks with AI agents?
AI agents introduce unique risks because they connect to sensitive databases, trigger third-party tools, and make real-time decisions autonomously.
- Prompt injection and goal manipulation
- Unauthorized data access and exfiltration
- Overprivileged tool permissions
- Lateral movement across connected systems
- Shadow agents created without IT oversight
Does Lasso discover AI agents built on cloud or third-party platforms?
Yes. Lasso provides platform-agnostic discovery across Vertex AI, Microsoft Copilot, AWS Bedrock, Salesforce Agentforce, and custom-built agents. It automatically inventories every agent in your environment regardless of which builder service was used.
What is AI Security Posture Management (AI-SPM)?
AI-SPM helps organizations implement secure-by-design policies for AI agents. It defines how agents should behave, what tools they can use, and which resources they're permitted to access, aligned with frameworks like OWASP, MITRE, and NIST.
How does Lasso handle non-deterministic AI agent behavior?
Lasso uses an intent framework purpose-built for AI agents. Since agents can take different paths to achieve the same goal, Lasso analyzes the underlying reasoning behind every action in real-time. This detects malicious deviations or goal misalignment even when the execution path changes.
What is the difference between monitoring and auditing for AI agents?
Monitoring is real-time detection and blocking of threats as they happen. Auditing is historical tracking of AI agent behavior for governance and compliance. Lasso provides both: live runtime protection at the intent layer plus persistent audit logs of every autonomous decision.
How does Lasso protect against prompt injection in AI agents?
Lasso decodes over 3,000 obfuscation techniques and detects threats at the intent layer. It blocks inputs designed to bypass safety guardrails or trick agents into performing unauthorized actions, even when attacks are hidden within seemingly approved content.
Can Lasso identify overprivileged or high-risk AI agents?
Yes. Lasso maps agents and visualizes their connections to third-party tools, databases, and internal services. It assigns risk scores based on attack surface, permissions, tool access, and data exposure so security teams know which agents require immediate attention.
How quickly can enterprises deploy AI agent security with Lasso?
Lasso deploys with a single line of code via Gateway, API, or SDK. Pre-built policy templates aligned to OWASP, MITRE, and NIST get you started immediately with no custom development required.
Keep up with Lasso
Securing Agentic AI: The Intent Security Framework


.avif)
